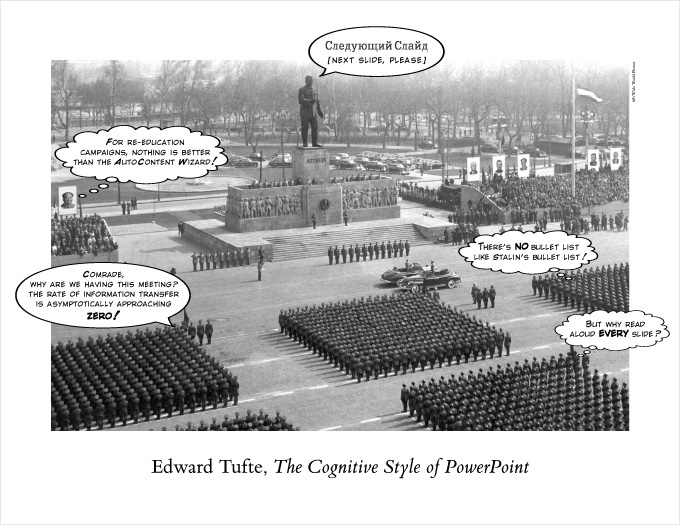
Some things don't change - what makes a good web appication
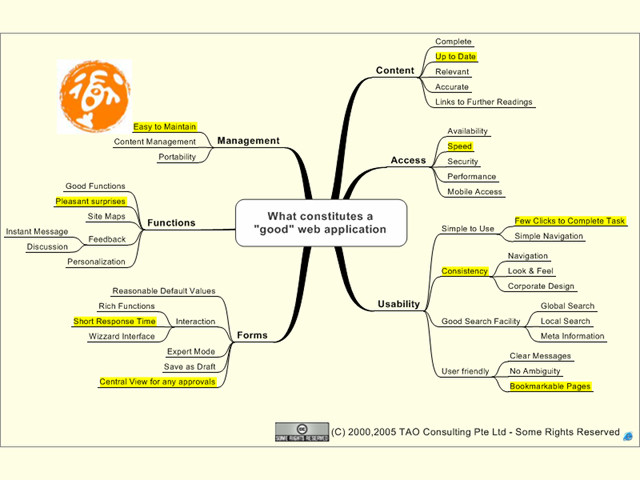
We just need to keep them in mind.
Posted by Stephan H Wissel on 31 May 2012 | Comments (1) | categories: Software
Usability - Productivity - Business - The web - Singapore & Twins
Posted by Stephan H Wissel on 31 May 2012 | Comments (1) | categories: Software
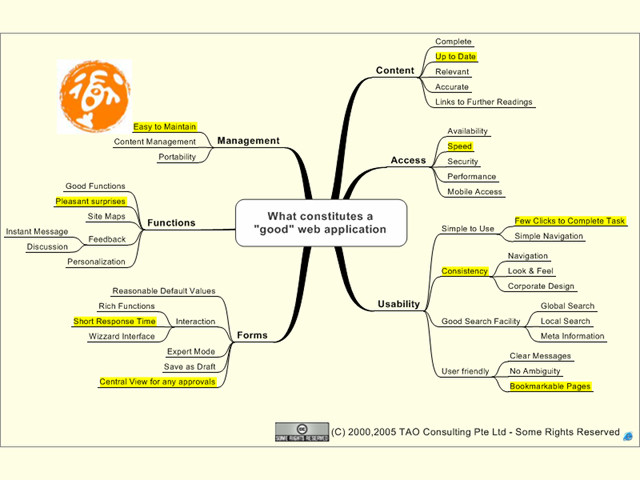
Posted by Stephan H Wissel on 30 May 2012 | Comments (0) | categories: Technology
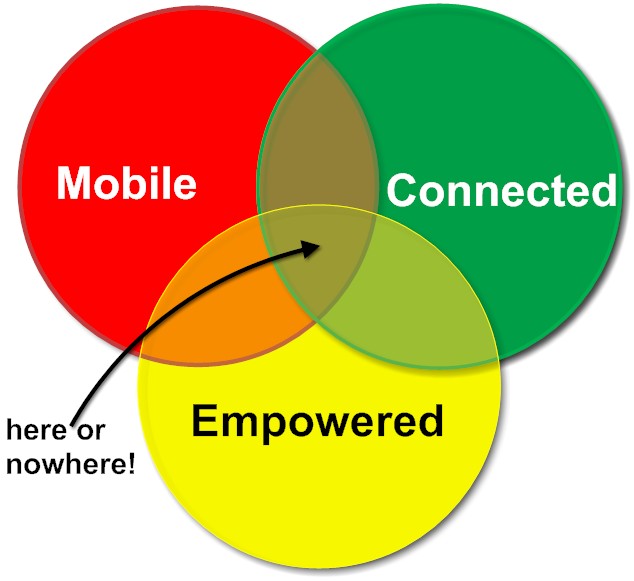
Posted by Stephan H Wissel on 24 May 2012 | Comments (0) | categories: SocialBusiness
Posted by Stephan H Wissel on 24 May 2012 | Comments (0) | categories: Software
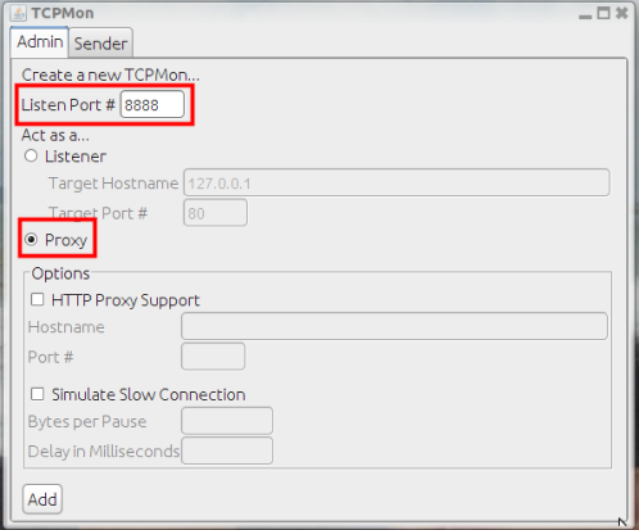
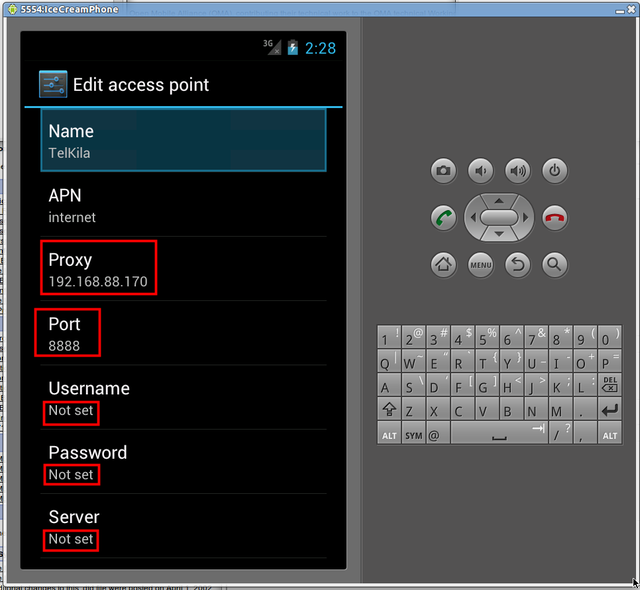
127.0.0.1:8888. Note: you need the real IP in the Android phone or emulator. The TCPMon screen then nicely shows the outgoing requests and incoming responses: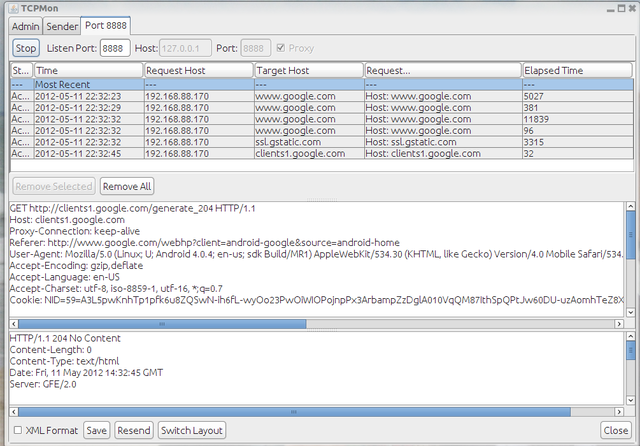
tools/android from the install directory to download and install the various versions of the Android OS Emulations from 1.0 all the way to 4.0.3. In the Tools menu you can manage your AVD (Android Virtual Devices) and configure different images. The emulator comes with the option of snapshots, quickstart, cold boot etc.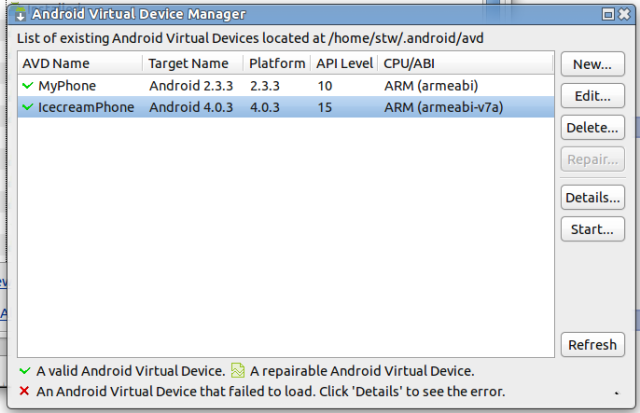
android-sdk-linux/tools/emulator -avd MyPhone -http-proxy 192.168.88.170:8888 and android-sdk-linux/tools/emulator -avd IcecreamPhone -http-proxy 192.168.88.170:8888 resulting in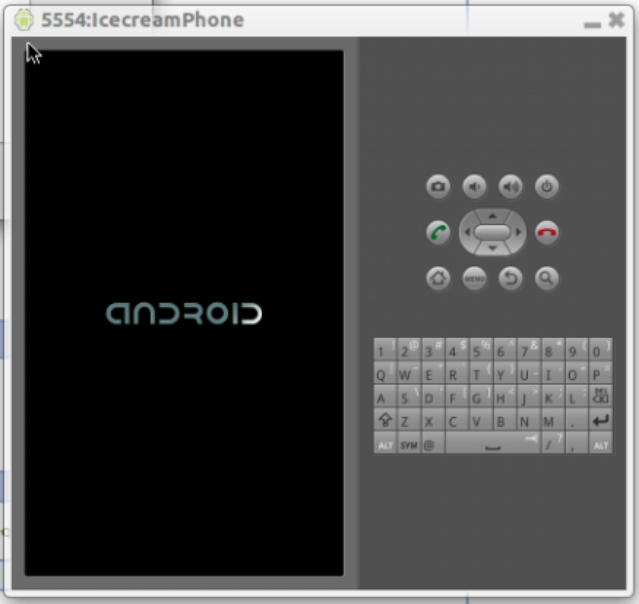
Posted by Stephan H Wissel on 13 May 2012 | Comments (0) | categories: Show-N-Tell Thursday
Posted by Stephan H Wissel on 10 May 2012 | Comments (0) | categories: Lotus
Posted by Stephan H Wissel on 10 May 2012 | Comments (0) | categories: After hours
Posted by Stephan H Wissel on 09 May 2012 | Comments (0) | categories: Business